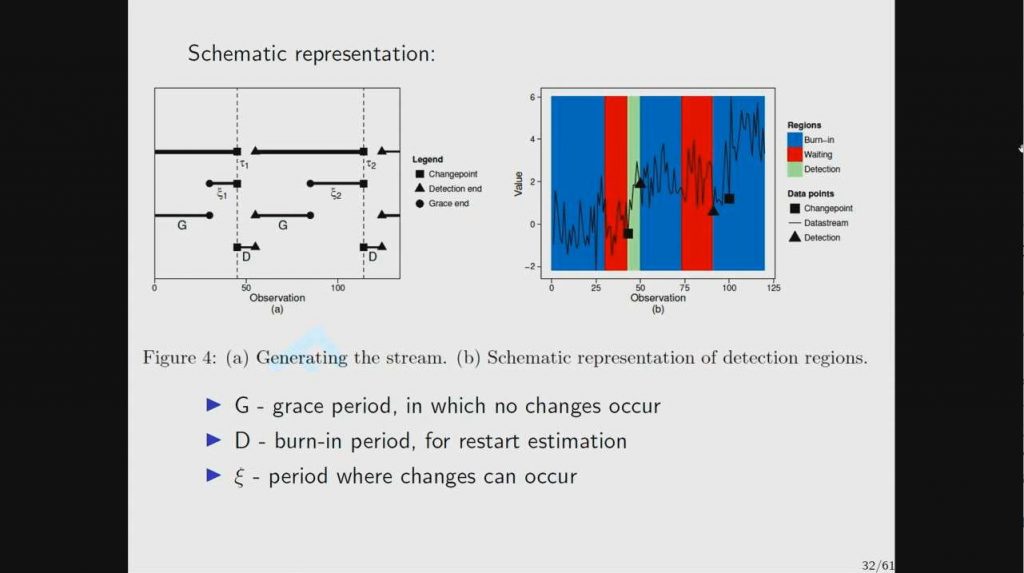
Unsupervised Streaming Cyber-Analytics
The supervised learning approach to cyber-analytics has proven rather successful. However, there are challenges with this approach, including a frequent dearth of labelled data, the issue of temporal variation, and fundamentally, problems of data volume…
Debugging Failures in Deployed Software
Software vendors like Microsoft received a huge number of crash reports every day. Our project tackles the challenges in effectively and efficiently triaging and diagnosing crash reports.
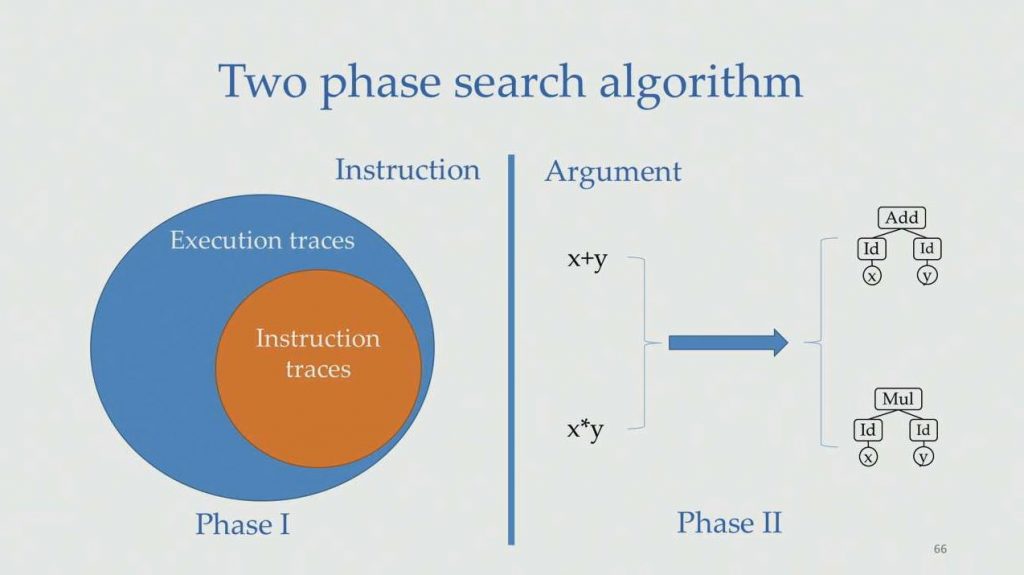
Neural Representations for Program Analysis and Synthesis
Representing a program as a numerical vector (i.e., neural representation) enables handling discrete programs using continuous optimization approaches, and thus opens up new opportunities to tackle many traditional challenging programming language problems. In this talk,…
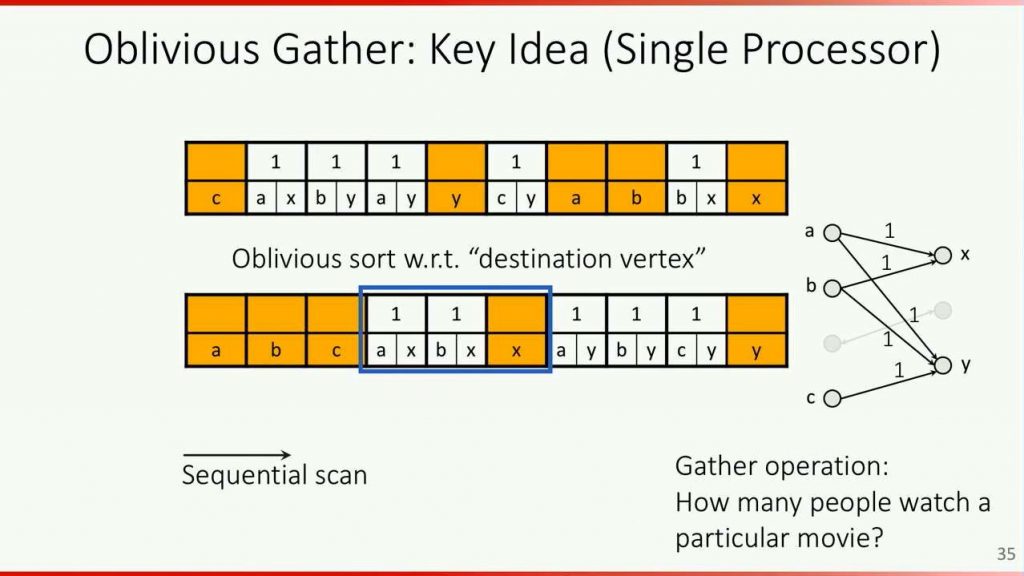
Using Efficient Oblivious Computation to Keep Data Private and Obfuscate Programs
Protecting sensitive user data and proprietary programs are fundamental and important challenges. For instance, when users outsource their private data to the cloud, they risk leakage of the data in the event of a data…
Homomorphic Encryption Standardization Workshop
The goals of this Homomorphic Encryption Standardization Workshop are to approve a draft standard for parameter selection for homomorphic encryption and revisit our initial API design standard. We welcome new participants who wish to be a part of…
DICE: Device Identifier Composition Engine
aka RIoT (Robust | Resilient | Recoverable – IoT) Introduction DICE (previously called RIoT) is a family of hardware and software techniques for hardware-based cryptographic device identity, attestation, and data encryption. DICE hardware requirements are…