Security operations
Explore the latest insights, tools, frameworks, and developments in security operations (SecOps).
Refine results
Topic
Products and services
Publish date
-
 Joy Chik, Microsoft CVP, Identity, explains how passwordless works and provides steps to begin preparing your organization to eliminate passwords.
Joy Chik, Microsoft CVP, Identity, explains how passwordless works and provides steps to begin preparing your organization to eliminate passwords. -

Changing security incident response by utilizing the power of the cloud—DART tools, techniques, and procedures: part 1
A series on DART’s tools, techniques, and procedures for investigating cybersecurity incidents at their customer organizations. -

Azure Sentinel updates: Improve your security operations with innovations from a cloud-native SIEM
Learn about all the new features and enhancements introduced in Azure Sentinel, Microsoft’s cloud-native SIEM solution, during Ignite 2019. -

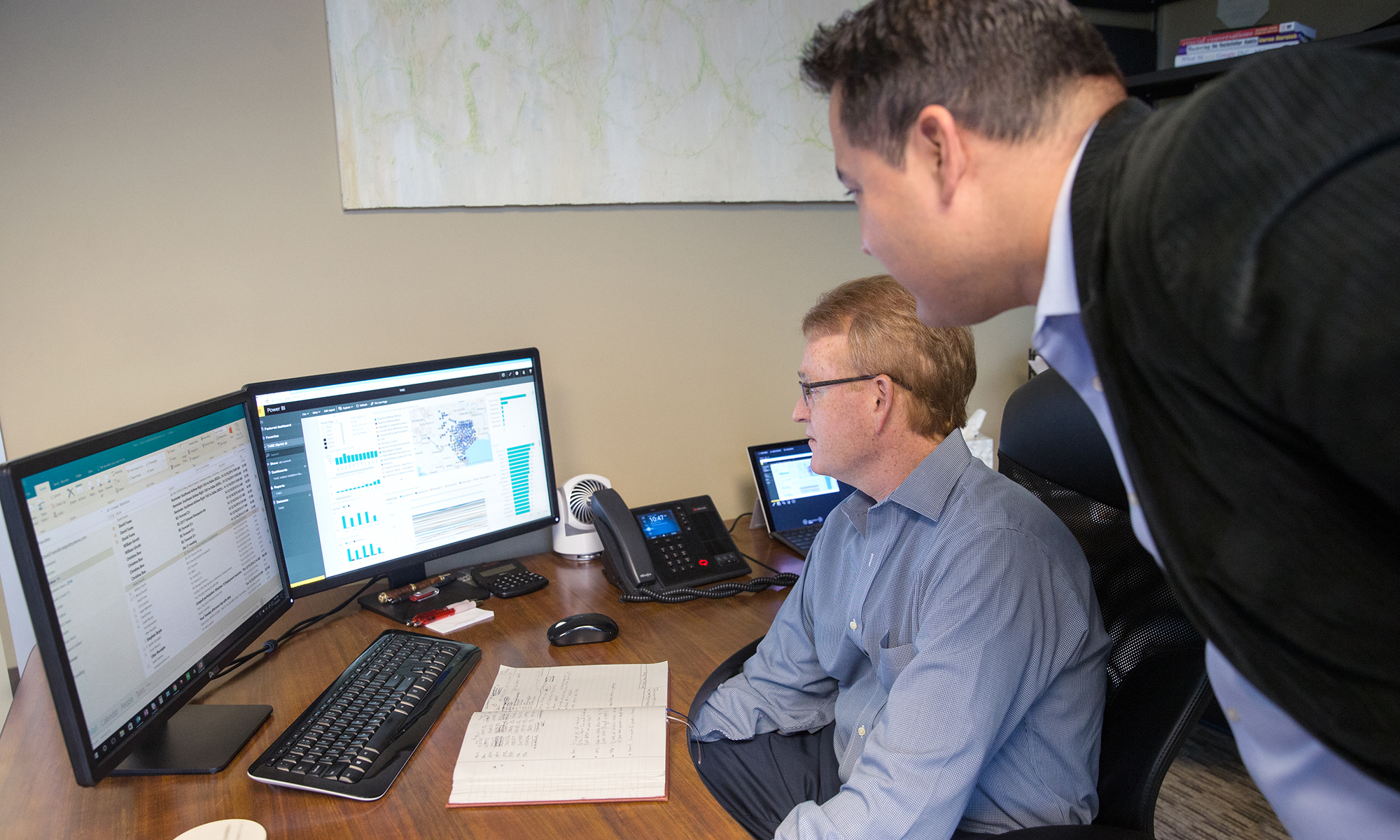
Microsoft’s 4 principles for an effective security operations center
Microsoft Chief Cybersecurity Strategist, Jonathan Trull, outlines four principles any organization can use to improve the effectiveness of its SOC. -

CISO series: Lessons learned from the Microsoft SOC—Part 3a: Choosing SOC tools
In the next post of our series, we provide tips on choosing technology to help a security operations center (SOC) be more responsive, effective, and collaborative. -

Rethinking how we learn security
To keep pace with cyberthreats and attract critical talent, we need to change the cyber learning paradigm. -

Improve security and simplify operations with Windows Defender Antivirus + Morphisec
Learn how Towne Properties uses Windows Defender Antivirus and Morphisec to protect against advanced memory-based attacks while simplifying operations. -
How to recover from a security breach
Actionable tips from security experts on how to prevent, mitigate, or recover from a cyberattack. -
Step 10. Detect and investigate security incidents: top 10 actions to secure your environment
The “Top 10 actions to secure your environment” series outlines fundamental steps you can take with your investment in Microsoft 365 security solutions. -
Step 9. Protect your OS: top 10 actions to secure your environment
The “Top 10 actions to secure your environment” series outlines fundamental steps you can take with your investment in Microsoft 365 security solutions. -

Executing on the vision of Microsoft Threat Protection
Learn about how we’re already executing on the vision of Microsoft Threat Protection—the premier solution for securing the modern workplace across identities, endpoints, user data, apps, and infrastructure. -

4 tried-and-true prevention strategies for enterprise-level security
Learn about the four cyber hygiene best practices recommended in the 24th edition of the Microsoft Security Intelligence Report (SIR) to help reduce your risk of attack.