Threat actors
Microsoft actively discovers and tracks threat actors across observed state-sponsored, ransomware, and criminal activities. Get insights from the 60 nation-state actors, 50 ransomware groups, and hundreds of other attackers we’ve tracked.
Refine results
Topic
Products and services
Publish date
-
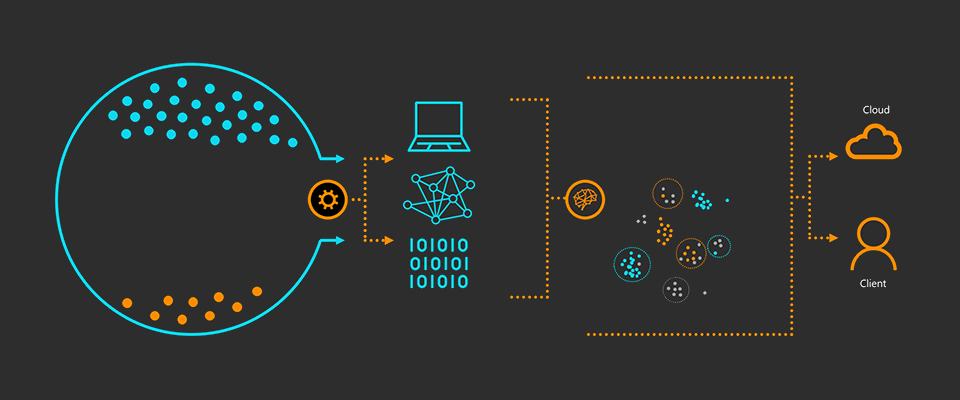
 Two new machine learning protection features within the behavioral blocking and containment capabilities in Microsoft Defender ATP specialize in detecting threats by analyzing behavior, adding new layers of protection after an attack has started running.
Two new machine learning protection features within the behavioral blocking and containment capabilities in Microsoft Defender ATP specialize in detecting threats by analyzing behavior, adding new layers of protection after an attack has started running. -

One simple action you can take to prevent 99.9 percent of attacks on your accounts
Learn about common vulnerabilities and what you can do to protect your company from attacks. -

New machine learning model sifts through the good to unearth the bad in evasive malware
Most machine learning models are trained on a mix of malicious and clean features. -
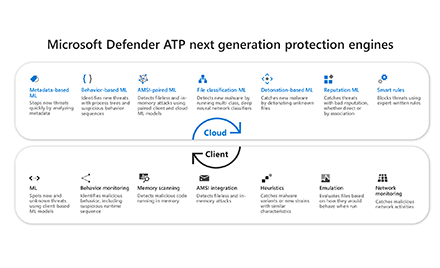
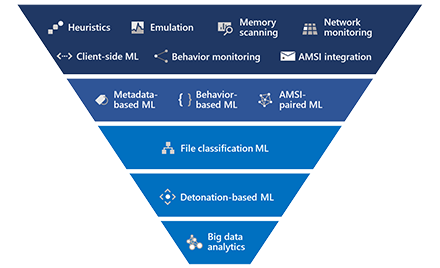
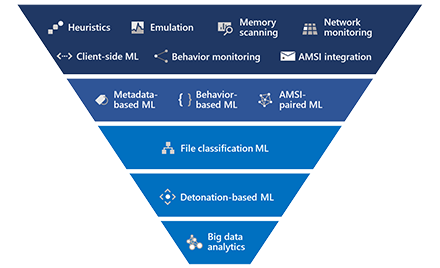
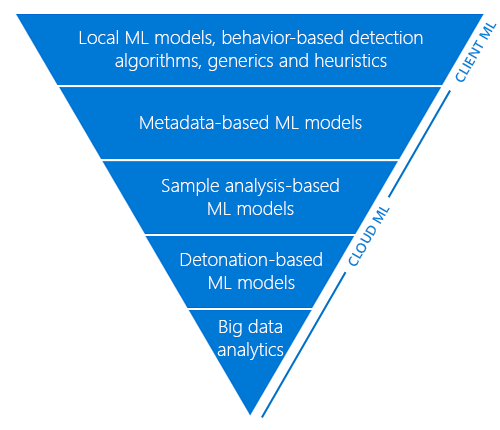
Inside out: Get to know the advanced technologies at the core of Microsoft Defender ATP next generation protection
While Windows Defender Antivirus makes catching 5 billion threats on devices every month look easy, multiple advanced detection and prevention technologies work under the hood to make this happen. -
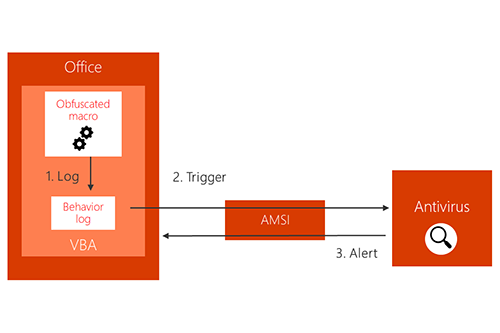
Office VBA + AMSI: Parting the veil on malicious macros
As part of our continued efforts to tackle entire classes of threats, Office 365 client applications now integrate with Antimalware Scan Interface (AMSI), enabling antivirus and other security solutions to scan macros and other scripts at runtime to check for malicious behavior. -
Protecting the protector: Hardening machine learning defenses against adversarial attacks
Harnessing the power of machine learning and artificial intelligence has enabled Windows Defender Advanced Threat Protection (Windows Defender ATP) next-generation protection to stop new malware attacks before they can get started – often within milliseconds. -
How artificial intelligence stopped an Emotet outbreak
At 12:46 a.m. local time on February 3, a Windows 7 Pro customer in North Carolina became the first would-be victim of a new malware attack campaign for Trojan:Win32/Emotet. -
Introducing Windows Defender Application Control
Application control is a crucial line of defense for protecting enterprises given today’s threat landscape, and it has an inherent advantage over traditional antivirus solutions. -
The two-pronged approach to detecting persistent adversaries
Advanced Persistent Threats use two primary methods of persistence: compromised endpoints and compromised credentials. -
Microsoft Security Intelligence Report: Strontium
The Microsoft Security Intelligence Report (SIR) provides a regular snapshot of the current threat landscape, using data from more than 600 million computers worldwide. -
Cleaning up misleading advertisements
Microsoft is committed to protecting our customers and their Windows experience.