Microsoft Defender
Microsoft Defender helps prevent, detect, and respond to attacks across devices, identities, apps, email, data, workloads, and clouds. Explore threat intelligence, capabilities, and real-world guidance to help you get more out of Defender.
Refine results
Topic
Products and services
Publish date
-
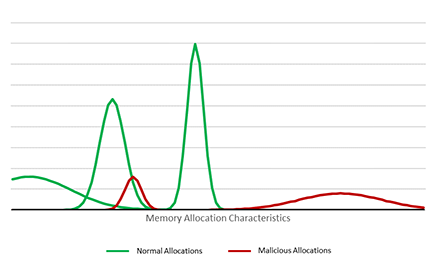
 Today’s attacks put emphasis on leaving little, if any, forensic evidence to maintain stealth and achieve persistence.
Today’s attacks put emphasis on leaving little, if any, forensic evidence to maintain stealth and achieve persistence. -
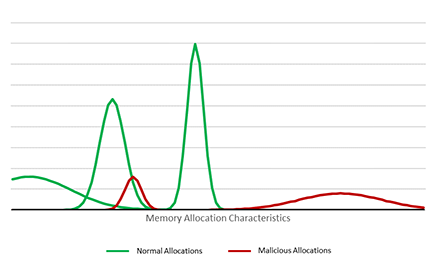
Windows Defender Exploit Guard: Reduce the attack surface against next-generation malware
Windows Defender Exploit Guard is a new set of intrusion prevention capabilities that ships with the Windows 10 Fall Creators Update. -
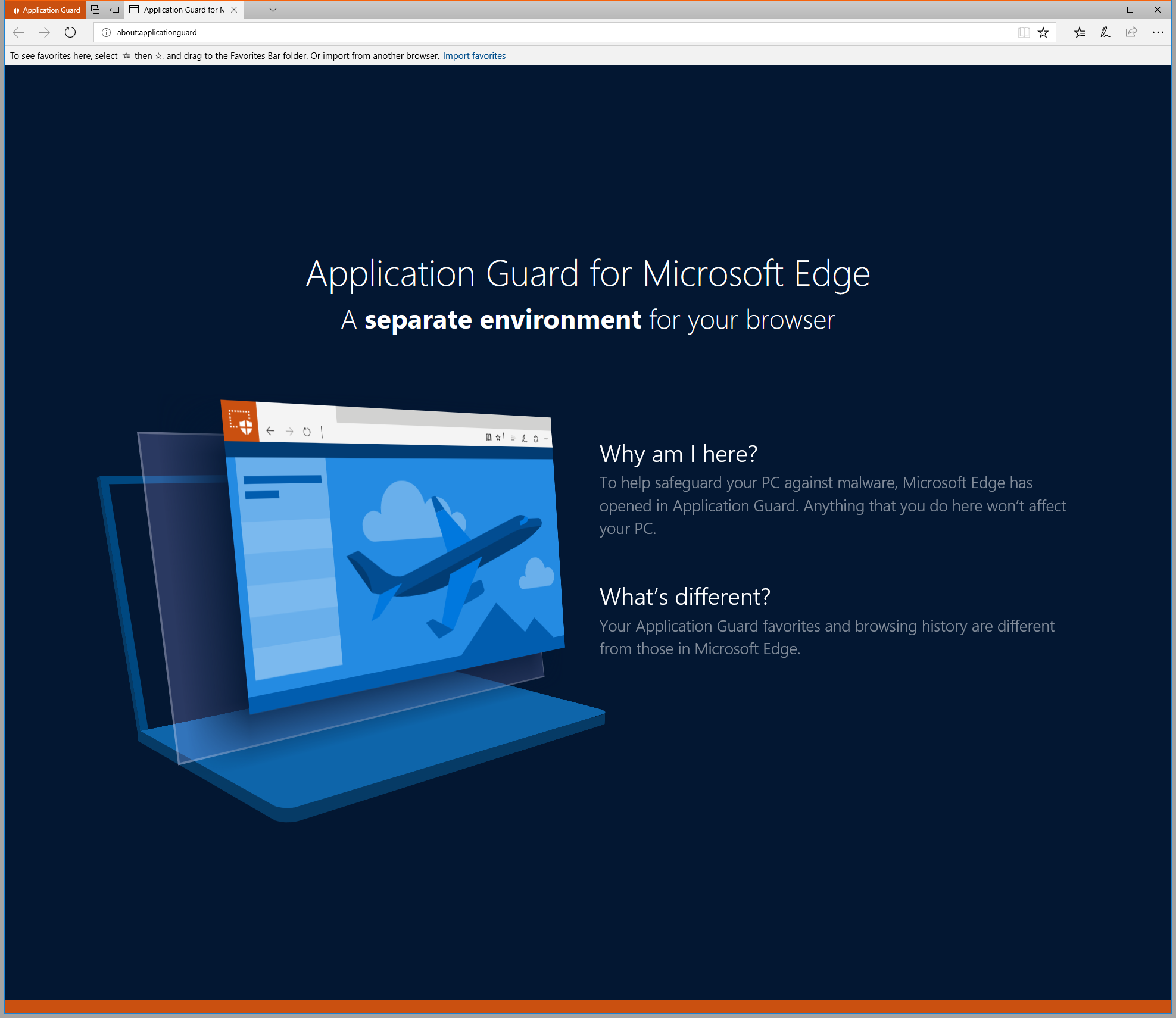
Making Microsoft Edge the most secure browser with Windows Defender Application Guard
Innovation in the attack space is constant as adversaries increase in both determination and sophistication. -
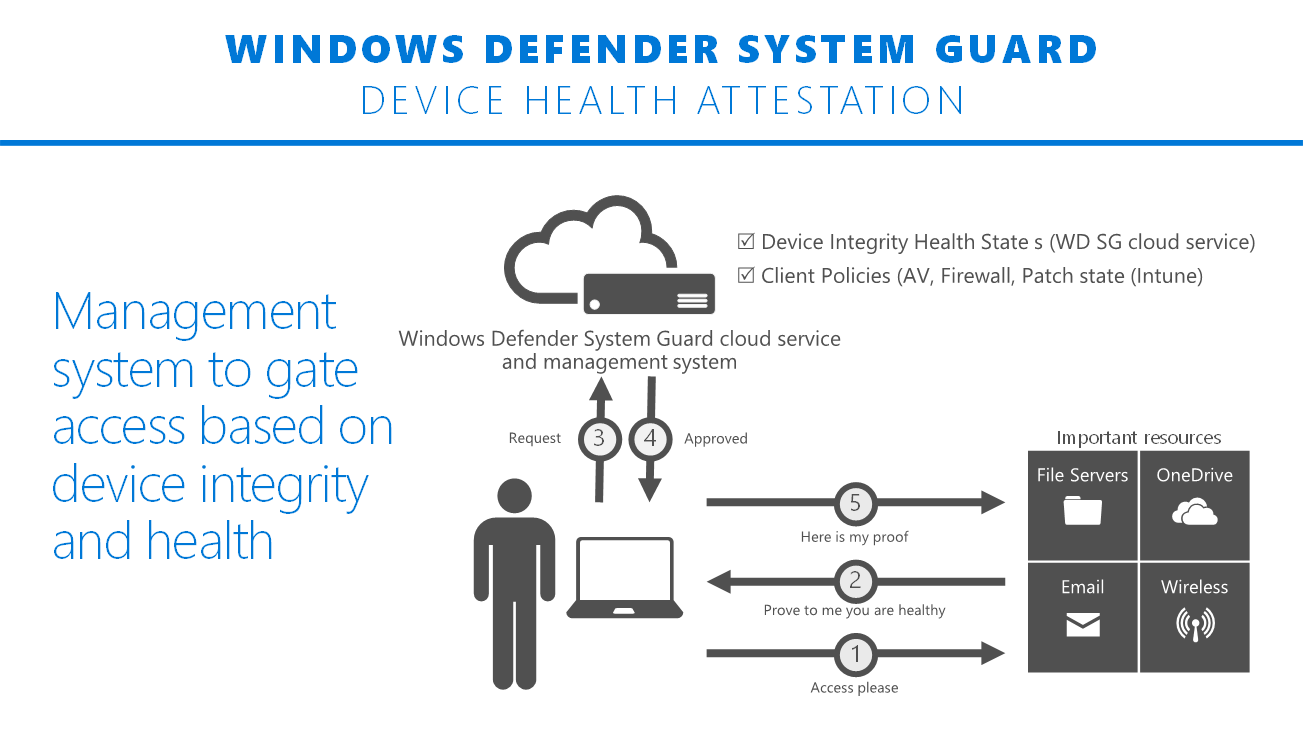
Hardening the system and maintaining integrity with Windows Defender System Guard
Just a few weeks ago at Ignite we announced Windows Defender System Guard, which ships in Windows 10, version 1709, also known as the Fall Creators Update. -
Advanced Threat Analytics security research network technical analysis: NotPetya
This post is authored by Igal Gofman, Security Researcher, Advanced Threat Analytics. -
Announcing the Windows Defender Advanced Threat Protection ISO 27001 audit assessment report
The security and privacy of customer data are our top priority. -

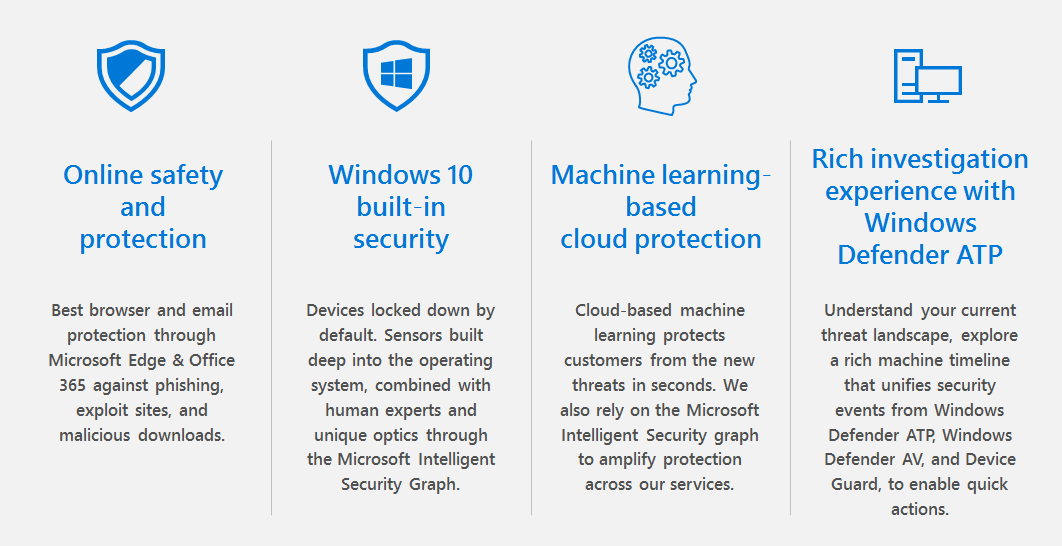
Stepping up protection with intelligent security
With digital transformation, technology becomes increasingly central to every business and organization. -
New Microsoft 365 features to accelerate GDPR compliance
Today we made several Microsoft 365 security and compliance announcements and updates as part of the news from the Microsoft Ignite conference. -

3 key tenets to help with security management
This post is authored by Berk Veral, Director, Product Marketing, Enterprise Cybersecurity Group. -
Ransomware 1H 2017 review: Global outbreaks reinforce the value of security hygiene
The trend towards increasingly sophisticated malware behavior, highlighted by the use of exploits and other attack vectors, makes older platforms so much more susceptible to ransomware attacks. -
Top 5 best practices to automate security operations
This post is authored by Jonathan Trull, Worldwide Executive Cybersecurity Advisor, Enterprise Cybersecurity Group.